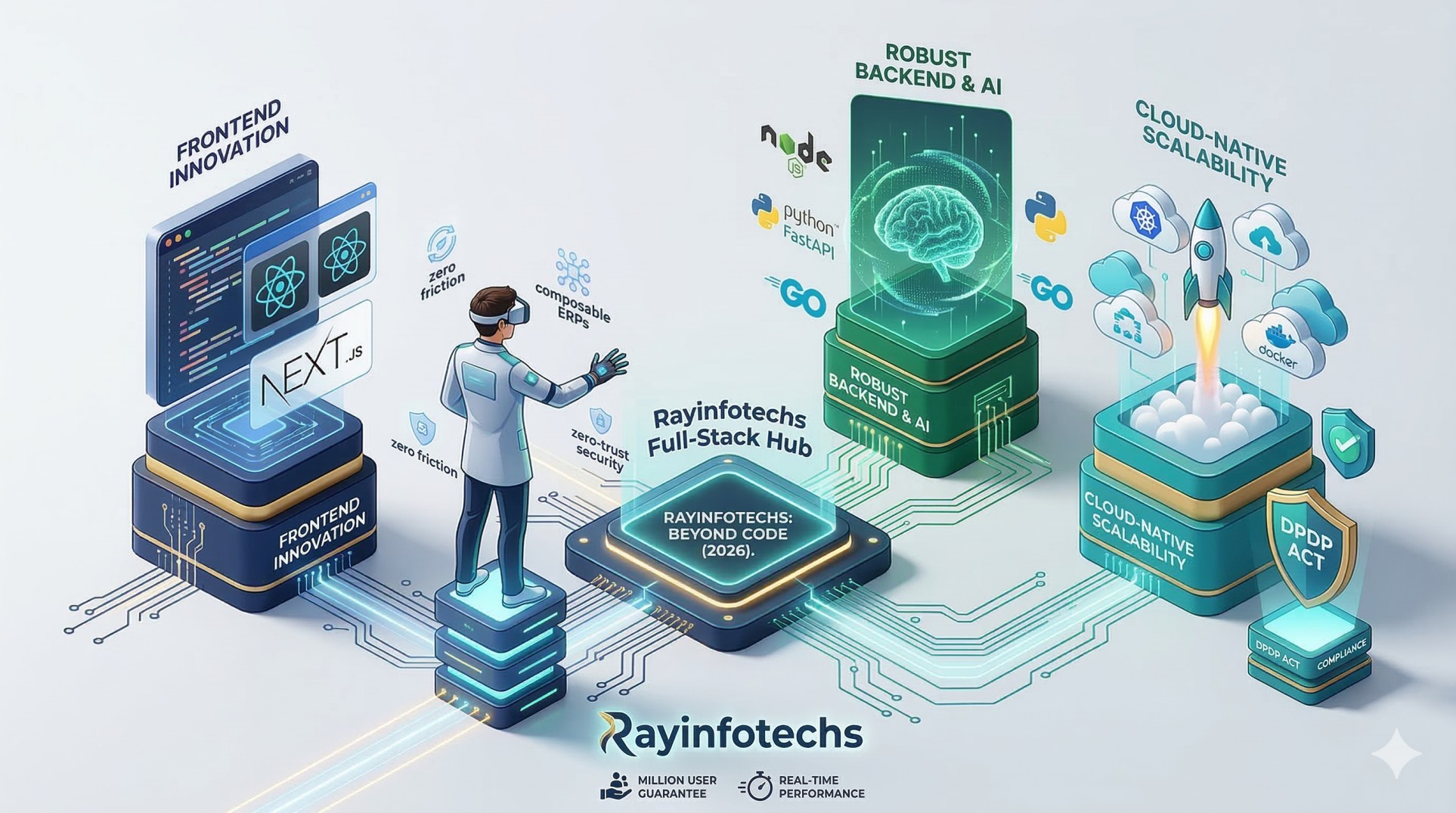
In 2026, the digital divide is no longer about who has an app, but whose software can think, scale, and adapt. While off-the-shelf SaaS products offer a quick start, they often become "digital straitjackets" as a business grows. At Rayinfotechs, we’ve see
In 2026, we don't just "add" AI; we build AI-Native software.
Autonomous Decision Engines: Custom software can now include proprietary models that automate complex approval workflows, fraud detection, and predictive inventory—features generic SaaS simply can't customize for your specific logic.
Predictive Maintenance: For our logistics and manufacturing clients, custom tools now predict equipment failure with 85% accuracy, saving millions in downtime.
Smart Dashboards: Forget static reports. We build interfaces that learn what metrics a CEO needs to see at 9:00 AM versus what a Manager needs at 4:00 PM.
Scalability used to take months of planning. At Rayinfotechs, we use a Cloud-Native, Microservices-first approach to ensure your software is "Infinite-Ready."
Modular Scaling: If your "Payments" module is under heavy load, our system scales only that part, saving you 30% on cloud costs compared to scaling a whole monolithic application.
Docker & Kubernetes Mastery: We containerize every custom application to ensure it runs flawlessly whether it's on AWS, Azure, or a private hybrid cloud.
With the Digital Personal Data Protection (DPDP) Act 2026 fully enforced, data security is now a legal survival skill.
Codebase Ownership: Unlike generic software where you share vulnerabilities with thousands of other companies, custom software provides an exclusive codebase, significantly reducing your "attack surface."
Privacy-by-Design: We bake compliance into the architecture. From automated data residency rules to role-based encryption, your custom tool ensures you are always "audit-ready" without manual effort.
 Live Test
Live Test